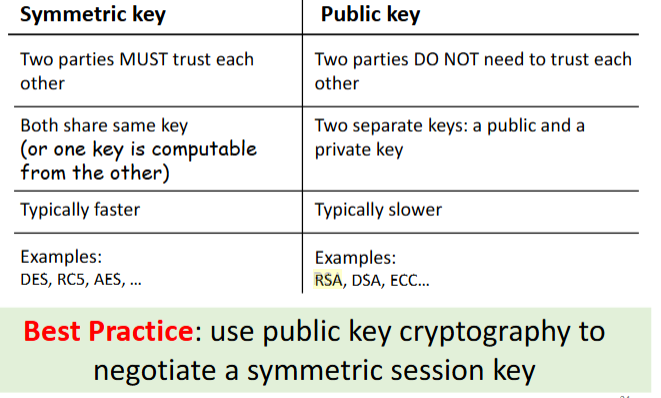
symmetric/asymmetric
public easier 2 nego key, symm is decentralized
- symmetric: Dependent on one key to encrypt/decrypt (one time pad)
- asymmetric: Private/public key TLS handshake, slower
- DES (Data Encryption Standard)
- Can be brute forced
- AES (Advanced Encryption Standard)
- Longer key sizes + safer + faster than DES
- Why do we need to use asymmetric crypto to negotiate a session key?
- Asymmetric encryption is slow, so it’s common to use asymmetric encryption to pass a symmetric encryption key to the other party and use something fast like AES to transfer data securely
Number theory
Modulo and Conguruent mod
- is the remainder of divided by , written Example:
- and are congruent modulo , written
, if
Example:
- relative prime
- 2 ints no common factors other than 1 aka gcd(a,b)=1
Mod proterties
- Commutative laws
- Associative laws
- Distributive law
Factoring
Example: Factor 84
is a factor
again
is a factor
7 is a prime → done
So:
Euler’s totient
Counts the numbers lesser than a number say n that do not share any common positive factor other than 1 with n or in other words are co-prime with n.
Formula:
- Let be the prime factorization of .
Examples
- ex factor
- Factor step
- Apply formula
- Hence 12 positive integers ≤ 36 that are coprime to 36.
- Factor step
- ex factor
- multiplicative inverses: just means reciprocal or
Extended Euclid’s algorithm
- GCD?
- Euclid’s algorithm (normal) Finds GCD of 2 ints
int EuclidAlgo(int m, int n){
if(n == 0) return m;
return greatestCommonDivisor(n, m % n);
}Euler’s Theorem
- For every and that are relatively prime
Example
, (which are relatively prime)
Verification:
Fermat’s Little Theorem
- If is prime
- and is a positive integer not divisible by ,
- then
Example
11 is prime, 3 not divisible by 11,
so
public key crypto
RSA (mod inverse thingy)
 Secure cos hard 2 factor large n
Secure cos hard 2 factor large n
- Length 2048 (see table if this differs that’s right)
- Encrypt w/ pub key, decrypt w/ private
- Auth: Sign w/ private, verify w/ public
- Algo:
- Receiver chose 2 large prime num & . Product, , = of public key
- Receiver calc & pick num relatively prime to . usu lrg tho can be as small as 3 will be the other half of the public key.
- Receiver calc mod inverse of mod . . = private key
- Receiver distribute both parts of public key: and . kept secret
Diffie-Hellman key negotiation
- nego shared secret over pub comms but DOES NOT provide auth!
- Both combine their secret keys to create new key
- A&B chose large prime & num s/t , can b public, A&B hv secret
- A sen B and B OPA
- A&B computes
- Ex
- and .
- A pick 42 & B 33
- A computes &B computes .
- Send results 2 e/o
- A recv 10, computes , & B computes done!
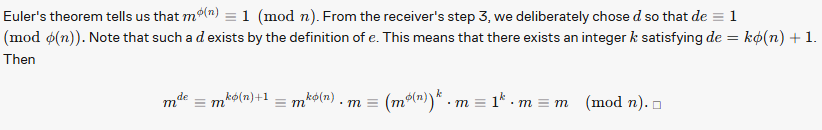
Proof
Esentially being asked to prove
where p is a prime number, g is a primitive root of p, and a and b are integers.
You can expand as by the definition of .
Then
Since all but the first of the terms in the binomial expansion contain a factor of ,
- discrete log problem
- Computing exponent “mod- base- logarithm” of but ! possible
- There is no known algorithm for efficiently computing discrete logs
Wat if w/ OTP?
- Agree on rand key?
- A gen random key w/ OTP key sen 2 B
- B get encrypt w/ OTP key :
sen to A - A decrypt msg w/ own key : , sen 2 B
- B do same rslt in same shared secrety key
Secure against open channel? No!
Open ca see all thre msg
- Rslt can compute:
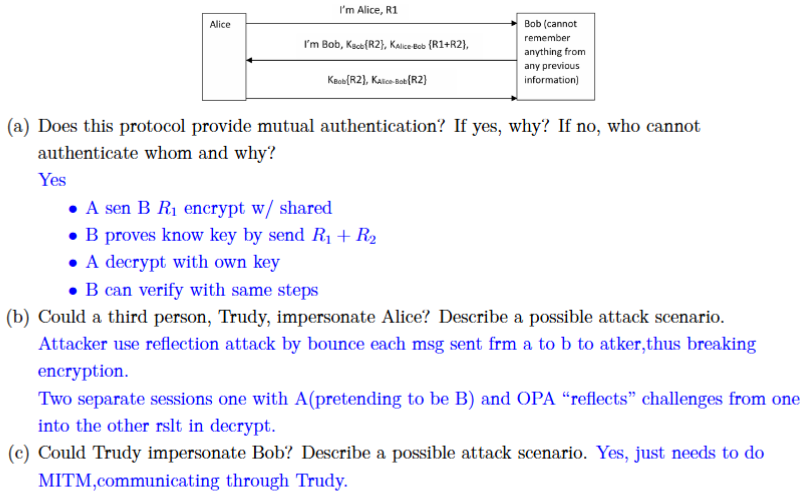
authy protocals
- 2 methods
- m1 1. A&B -m rand nonce encrypt w/ B pub key: (2 rounds) 2. Sesh key derived as , whr = hash func 3. atker need 2 find A&B 2 get & , resilient vs single-pt fail.
- m2
- A&B perform DH key exchange rslt in shared secret
- A&B sign the quantities they send (e.g., and ) w/ private keys
- Forward secrecy of DH w/ auth frm digital sigs, prot vs MITM
- mutural authy, Both parties prove e/o, req sesh key estab
- reflect atk
- prevent: make A&B hv diff challenge
- initiator 1st 2 prove id
- MUST distinguish between initiator and responder (directionality)
- Old keys must not be used, keys linked tgt
- MITM
- attacker constructs patterns that propagate from both ends to the middle of the cipher, in some cases by partial key-guessing
KDC/PKI (no need full steps)
Literially just key infrastructure they dont rly do anything else, no decryption, no telling u what keys to use etc
- Key Distribution Center (KDC)
- Representative solution: Kerberos
- Use Secret key cryptography
- Simplier but single point of fail
- all usrs must trust kdc
- easily scale, centralized key management
- Public Key Infrastructure (PKI)
- Based on public key cryptography
- contains:
- digital cert aka pub key cert
- Private key tokens
- Registration authority,Certification authority
- Certification management system
- disadvantages
- Speed, Private Key Compromise, expesive setup but cost effective long run.
- relies on relies on Certificate Authorities to issues/manage\
Digital certs
- Certificates issued by PKI Digital certificates vs digital signature
- certs issued by PKI CA validate pub key+id
- signatures auth+ prot usr msg. Small amnt of usrs can issue these certs, centralized
Needham Schroeder protocol
- cryptographic protocol used for mutual authentication and establishing a shared secret key between two parties
- 2 methods
- PGP
- (A identifies itself and sends a nonce, encrypted with B’s public key)
- B proves receipt of N_A and sends its own nonce back
- A confirms receipt of N_B, proving it’s alive
- KDC
- requests session key to communicate
- KDC replies with session key and ticket
- A forwards the ticket to B
- B challenges A with a nonce encrypted using session key
- A proves knowledge of session key by modifying and returning nonce
- PGP
Kerberos
- Goals: User server mutual auth
- auth once to service multiple servers
- scale to large n of users/servers
- belong to KDC
- uses only secret key (3DES/AES)
- alice auth ot kdc, server
SSL/TLS
how shit comms w/ e/o in web
- Secure Sockets Layer and Transport Layer Security protocol
- Handshake protocal
- PPG, shared secret btwn both usrs
- Record protocal
- Use shared secret 2 estab tunnel
- symmetric encryption (like AES) and MACs, does encryption aft handshake
- Handshake protocal
- TLS = upgraded ver of SSL
- One round trip → lower latency, encrypted handshake, modern ciphers Autonav port numbers (implement later with websockeet)
- Port 80 = HTTPw/ TCP, Port 443 = HTTPS
Other stuff
Homomorphic Encryption
- motivation and applications?
- arbitrary operations (such as addition or multip
- lication) apply 2 encrypted data (note that RSA CANNOT do multiplication and hence not fully homomorphic)
- need to perform computations on encrypted data without decrypting it
- basic operations
- Why do we need to add noise, and how to do the noise-deduction
- Noise results in GCD attack not working or any attack
- Noise is small term added into the ciphertext while encrypting.
- decryption function does not work if the noise is greater than a certain maximum value
- bootstrapping (noise-deduction) is applying the idea (due to Gentry) of homomorphically evaluating the decryption operation using an encryption of the secret key.
- Fully resets noise, high cost
- homomorphically decrypts a ciphertext and re-encrypts it—effectively resetting the noise
Tor
- What information could be disclosed when you visit a website?
- identity,apps/browsers/device/location/activity/data
- What’s Tor?
- client proxy
- NSA can track down and see people who use it
- what crypto Tor uses?
- SHA-1, SHA-256, and SHA3-256
- Why can Tor hide some information?
- First node still knows ur IP! (guard node)
- randomly selected nodes within the Tor network
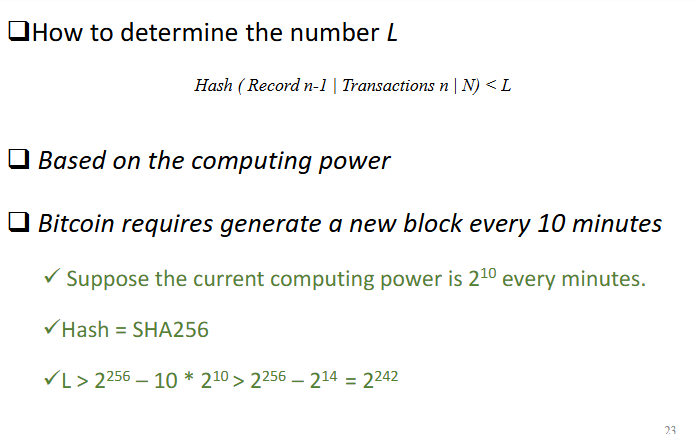
Block chain
- Proof of work? (central idea)
- solution that is difficult to find but is easy to verify
- solution that is difficult to find but is easy to verify
- Basic architecture, centralized or distributed?
- distributed system need to agree on following:
- initial sys state
- history of transactions
- current sys state
- Blockchain gets the functionality of a CA, withoutneeding a CA
- Blocks = recorded data, hashed chain = connectors
- 2 parties solve same time? Node finds best solution to N makes them winner
- distributed system need to agree on following:
Sample Qs
Section 1
- Which of the following is NOT computationally difficult? Verifying large primes
- What is false abt tor netowrk?
- No tor node can know ur IP (first node knows)
Section 2
1.
We want to find such that .
Try small values:
Answer:
2.
Factor:
Step 1: Mod 5
Step 2: Mod 11
Step 3: Chinese Remainder Theorem
Find such that:
and
Try :
Answer:
3.
Since (distinct primes):
Answer:
4.
Use the Euclidean Algorithm:
Answer: